What operational assurance
looks like in practice.
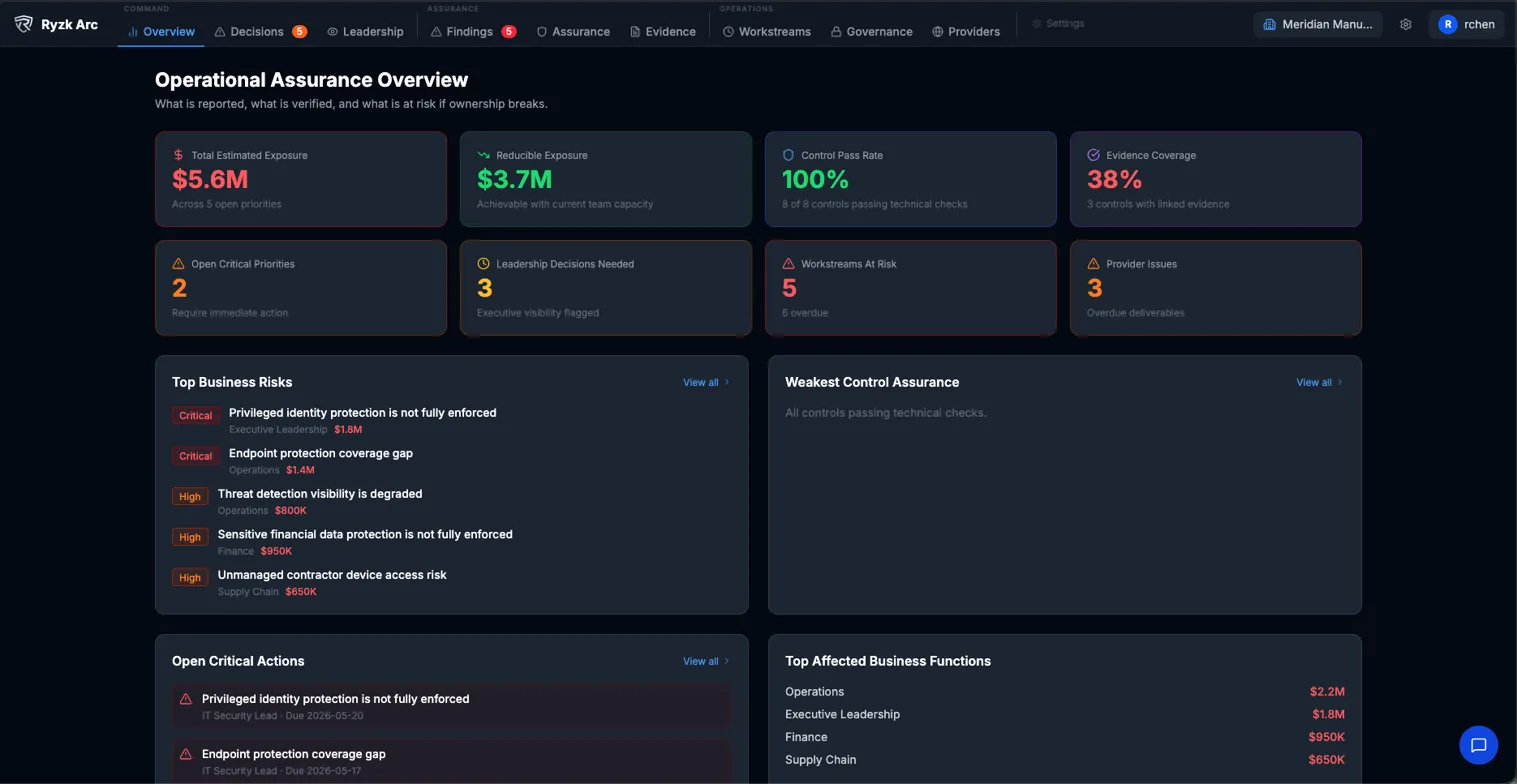
Every risk is tied to ownership, evidence, and accountability. This is what IT and security operations look like when the organization retains operational memory.
Ryzk Arc — Operational Assurance Intelligence · 28 Critical · Accelerating ↓ · 5 anomalies detected · Meridian Manufacturing Group